Endpoint Security Solution: Palo Alto Cortex XDR
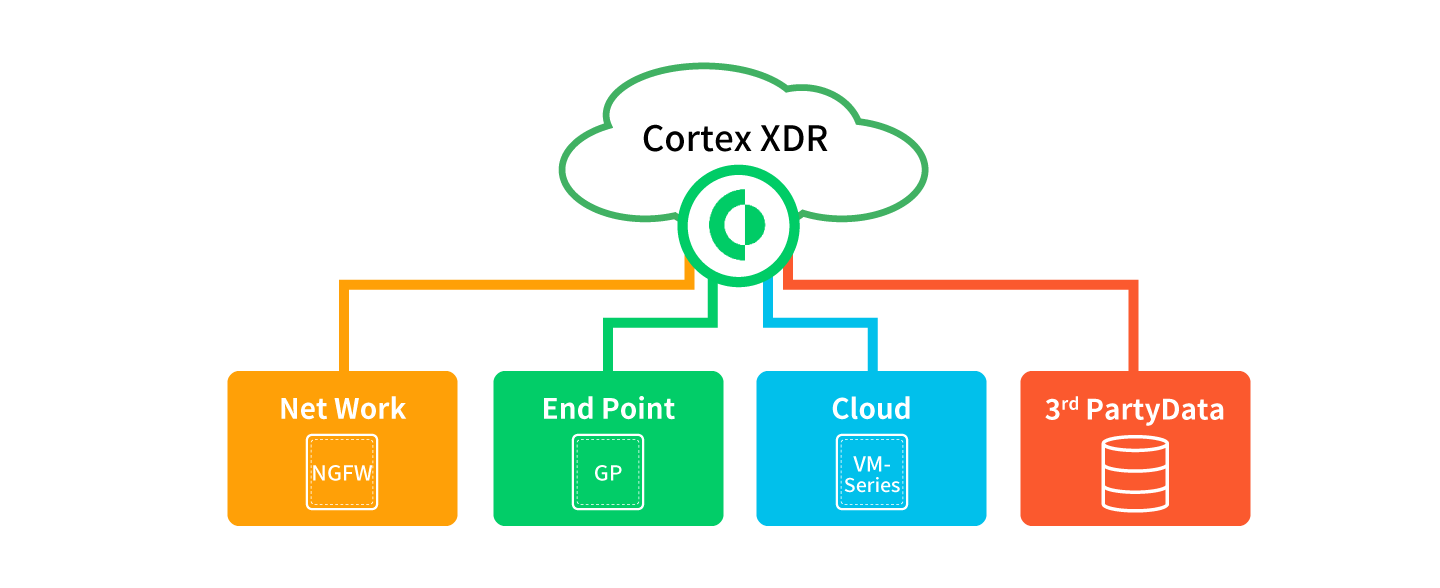
Palo Alto Networks's Cortex XDR is available as a managed service. Combined with superior detection results, reduce the number of security operation tasks while improving their effectiveness, using AI that learns from the abundant data available in networks, endpoints, and cloud nodes.
Palo Alto Cortex Highlights
Integrates companywide security operations from endpoints to platforms, increasing productivity and enhancing detection and response.

Entire-platform protection
Integrated siloed security management provides comprehensive visibility and response from devices to platforms.

Leverage machine learning for world-class threat
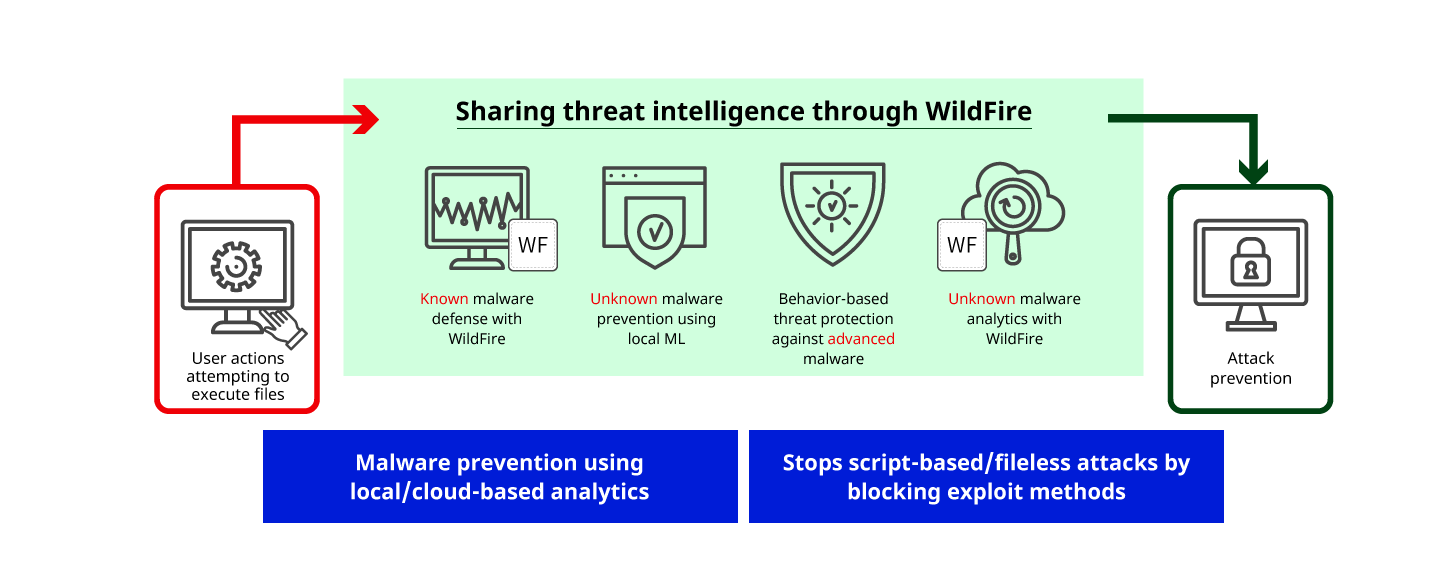
Protects devices with a multilayered defense that prevents known and unknown malware, fileless attacks, and exploits by leveraging various data sources.
Proactive incident detection and first response
In addition to alert-based detection and notification, the security team identifies incidents, interrupts communications, and quarantines devices.
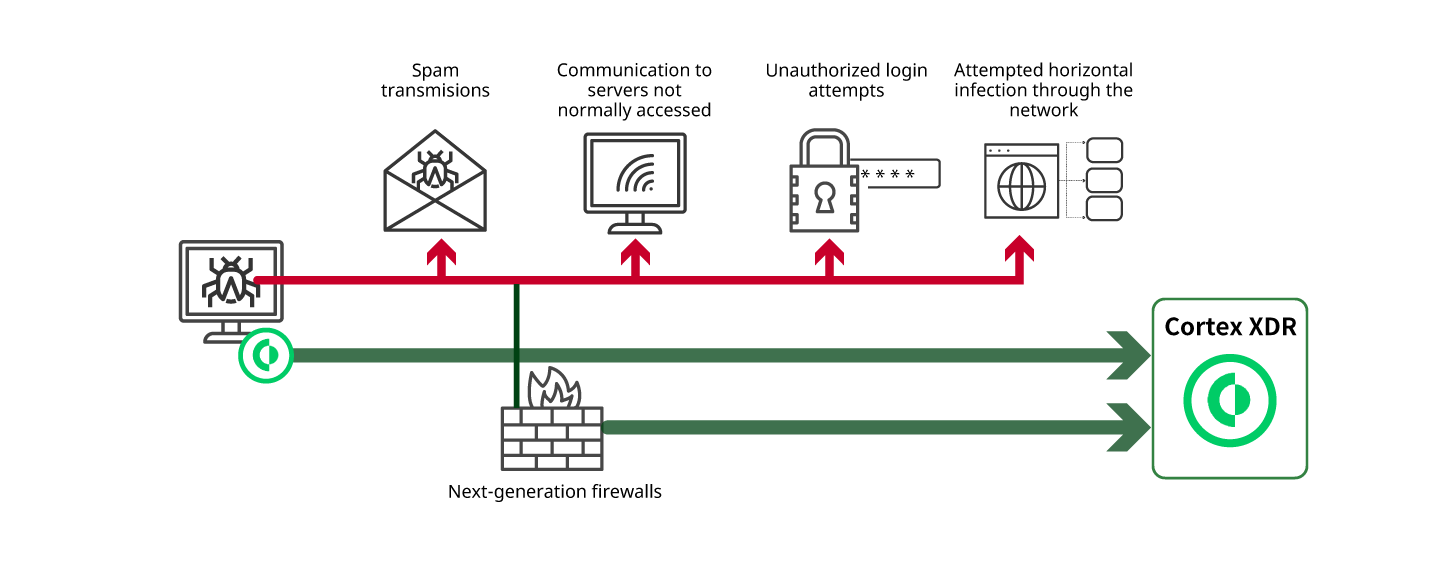
Machine learning-based threat detection addresses unknown threats that conventional endpoint security products cannot protect against.
Conventional antivirus software takes more than two to three days for signature matching (collecting specimens, analyzing them, and creating signatures). However, using Palo Alto’s Cortex XDR makes WildFire, a cloud-based sandbox engine, available. This engine analyzes all unknown attacks in the cloud and creates signatures to stop unknown malware infections within minutes.
Integrate siloed data and products
Integrate siloed (stacked and isolated) security product data and automate correlation analysis using machine learning technology to improve the efficiency of security operations. Support is available for Palo Alto’s FW, as well as for third-party products.
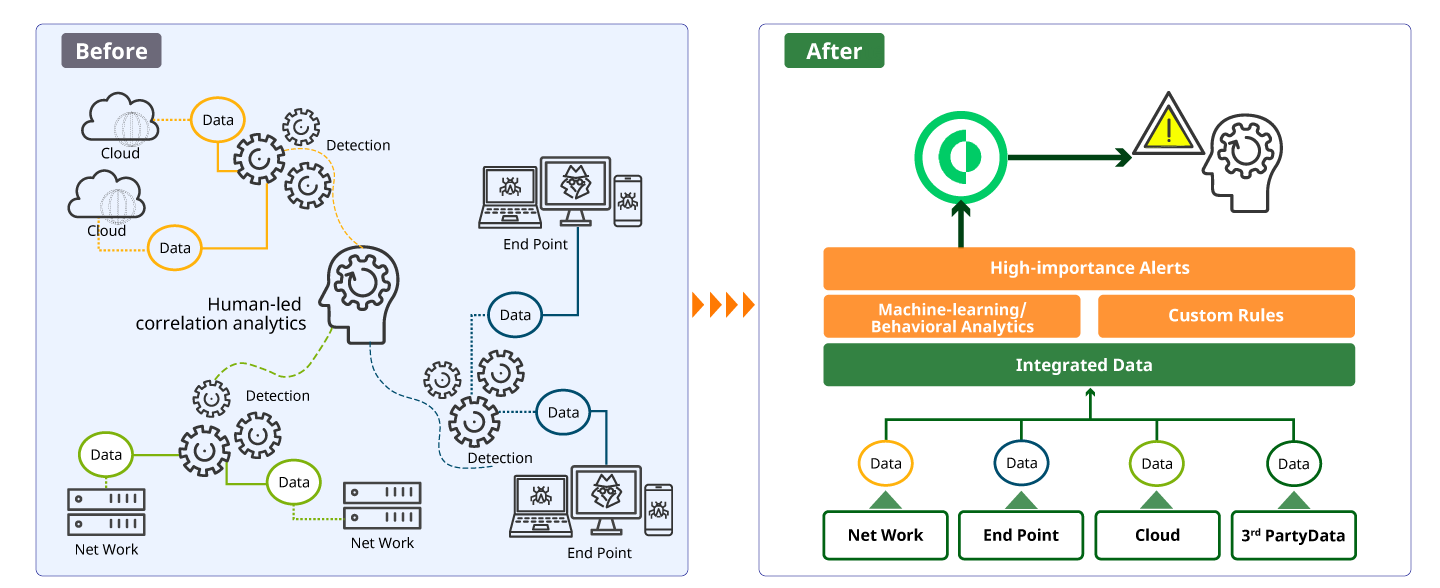
Patented behavioral analytics technology
Real-time device/user behavior learning on the cloud enables analyses that compare behavior with other devices and users. These analytics allow administrators to detect behaviors after malware infections and internal fraud and respond to these malicious activities in real time.
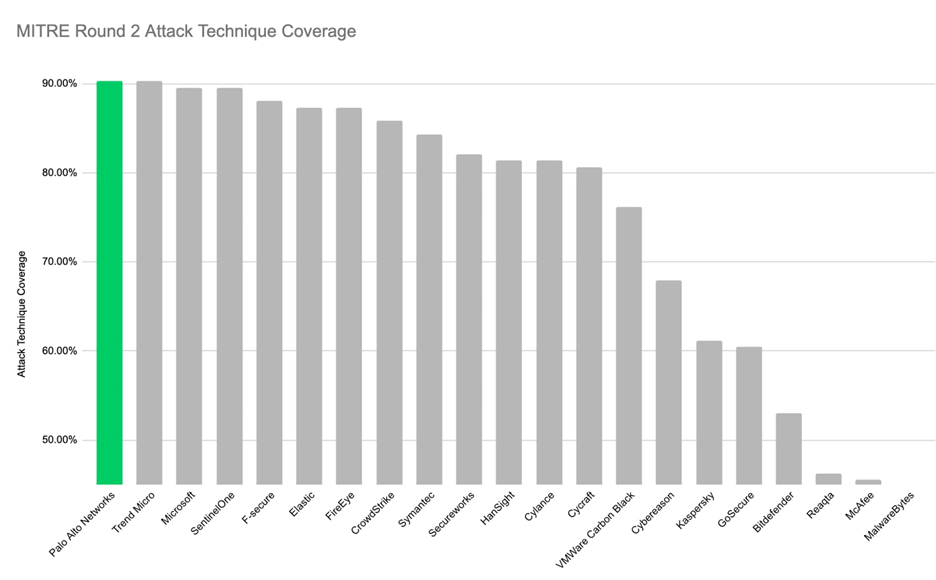
High ratings from third-party organizations
Scored higher than any other product in MITRE ATT&CK, a framework for organizing and systematizing cyberattack tactics and techniques by attack lifecycle, from the US non-profit research organization MITRE.